Core Concepts
Reference
Troubleshooting
Feedback
Database Credentials
When you provision a Database on Aptible, you'll be provided with a set of Database Credentials.
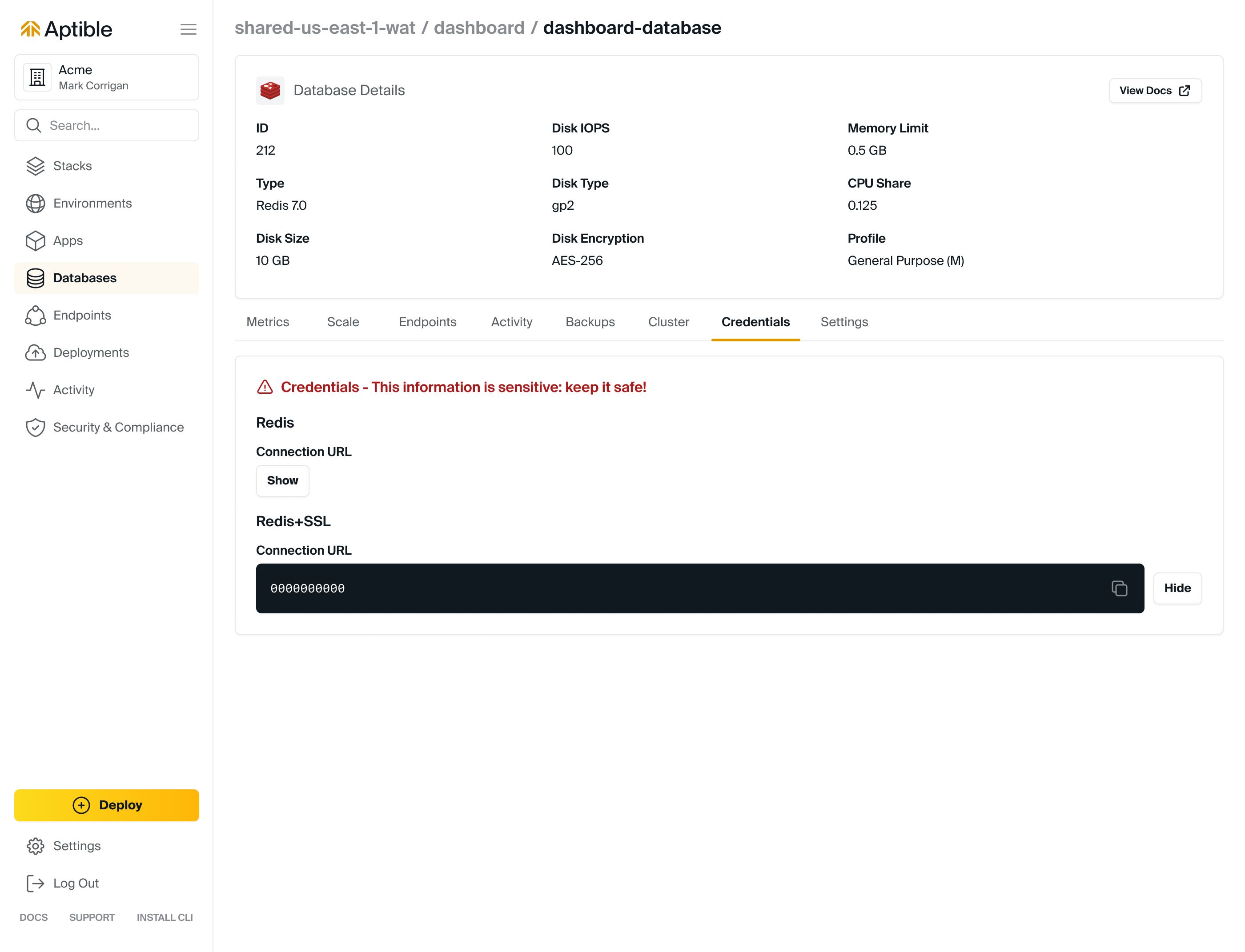
Accessing Database Credentials
Database Credentials can be accessed from the Aptible Dashboard by selecting the respective Database > selecting "Reveal" under "Credentials"
Using Database Credentials
Database Credentials are presented as connection URLs. Many libraries can use those directly, but you can always break down the URL into components.
The structure is:
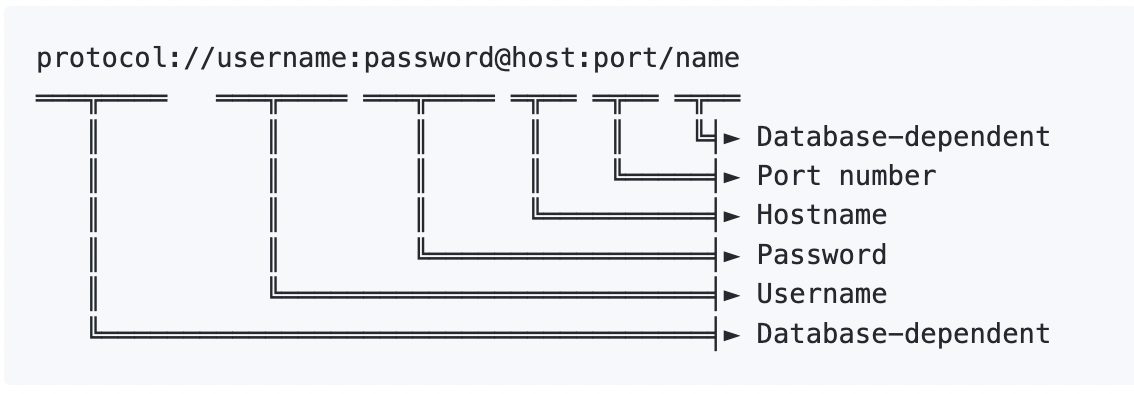
❗️ The password in Database Credentials should be protected for security.
There are three ways to connect to a Database using Database Credentials:
- Direct Access: This set of credentials is usable with Network Integrations. This is also how Apps, other Databases, and Ephemeral SSH Sessions within the Stack can contact the Database. Direct Access can be achieved by running the
aptible db:urlcommand and accessing the Database Credentials from the Aptible Dashboard. - Database Endpoint: Database Endpoints allow users to expose Aptible Databases on the public internet. When another Database Endpoint is created, a separate set of Database Credentials is provided. Database Endpoints are useful if, for example, a third party needs to be granted access to the Aptible Database. This set of Database Credentials can be found in the Dashboard.
- Database Tunnels: The
aptible db:tunnelCLI command allows users to create a Database Tunnel, which provides a convenient, ad-hoc method for users to connect to Aptible Databases from a local workstation. Database Credentials are exposed in the terminal when you successfully tunnel and are only valid while thedb:tunnelis up. Database Tunnels persist until the connection is closed or for a maximum of 24 hours.
📘 The Database Credentials provides credentials for the aptible user, but you can also create your own users for database types that support multiple users such as PostgreSQL and MySQL. Refer to the database's own documentation for detailed instructions. If setting up a restricted user, refer to Aptible's community topic for extra considerations.Note that certain Supported Databases provide multiple credentials. Refer to the respective Database documentation for more information.
Rotating Database Credentials
The only way to rotate Database Credentials without any downtime is to create separate Database users and update Apps to use the newly created user's credentials. Additionally, these separate users limit the impact of security vulnerabilities because applications are not granted more permissions than they need.
While using the built-in aptible user may be convenient for Databases that support it (MySQL, PostgreSQL, MongoDB, Elasticsearch 7). Aptible recommends creating a separate user that is granted only the minimum permissions required by the application.
The aptible user credentials can only be rotated by contacting Aptible Support. Please note that rotating the aptible user's credentials will involve an interruption to the app's availability.